This quick reference page provides a summary of the specifications of these topologies. For a complete reference including installation details, please refer to the Palo Alto Firewall Essentials Pod Planning and Installation Guide .
Want to watch the installation performed? Please see the video version of the installation guide.
The Palo Alto Networks Academy Firewall Essentials lab set is designed to have Internet access.
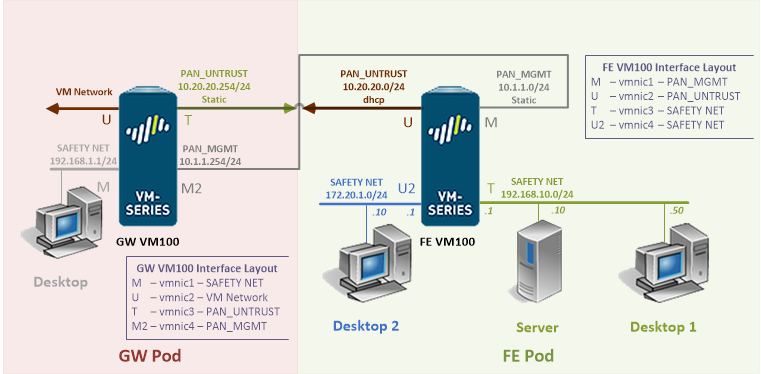
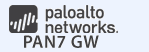
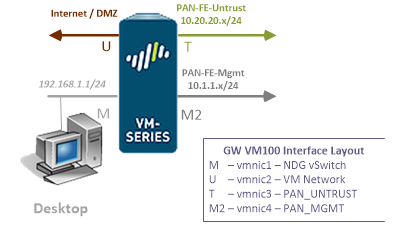
Due to this requirement, 2 topologies are needed. The Firewall Essentials Gateway pod (GW) is designed to provide Internet access to underlying Firewall Essentials pods (FE) per host.
To install and use these pods on your NETLAB+ system, you are required to indicate your acceptance of the NETLAB+ Pod Internet Access and Use Agreement.
Your system will not be enabled to support Palo Alto Networks Firewall Essentials pods until the agreement is accepted.
| Topologies | Supports | Documentation |
|---|---|---|
|
Palo Alto Firewall Essentials Planning and Installation Guide |
You may request virtual machine templates for the Palo Alto Firewall Essentials FE Pod and the Fire Essentials GW Pod from CSSIA.
The virtual machines in the pod are listed in the table below.
| Virtual Machine |
|---|
| GW Firewall |
| Desktop |
The virtual machines in the pod are listed in the table below.
| Virtual Machine |
|---|
| FE Firewall |
| Desktop1 |
| Desktop2 |
| Server |
For a step-by-step look at the installation process, see the video version of the installation guide.
The virtual machines are made available as Open Virtualization Format (OVF) or Open Virtualization Archive (OVA) files. These files are available for download from EPNC (Education Pathway National Center).
To request access to the preconfigured virtual machine templates from EPNC: